Home » Industry Watch » The Technological
Sixty Second MacBook Hack
Johnny Cache and David Maynor were to demonstrate today how you can hack a MacBook and get root in sixty seconds - remotely. Word has it they replaced default drivers with their own but still chose the MacBook because of what they called the 'Mac user base aura of smugness on security.'
'We're not picking specifically on Macs here, but if you watch those 'Get a Mac' commercials enough, it eventually makes you want to stab one of those users in the eye with a lit cigarette or something', said David Maynor.
Jon Ellch aka Johnny Cache is coauthor of Hacking Exposed Wireless. Brian Krebs has two posts about the event here and here.
One of the dangers of this type of attack, says Krebs, is that a machine running a vulnerable wireless device driver could be subverted just by being turned on. The wireless devices in most laptops - and indeed the Macbook targeted in this example - are by default constantly broadcasting their presence to any network within range, and most are configured to automatically connect to any available wireless network.
According to Maynor and Ellch, this attack can be carried out whether or not a laptop connects with a wireless network. It's enough for a machine to have its wireless card active for such an attack to be successful. That's a trivial demand, given that most wireless devices embedded in laptops these days are switched on by default and are configured to continuously seek out available wireless networks.
Because the software that powers wireless devices operates at a low level, traditional system safeguards like firewalls and antivirus software most likely won't be of much help. A system running poorly designed device drivers is open to attack just by doing what it's programmed to do.
These wireless device drivers are largely developed and written by an odd mix of hardware and software developers in an environment where 'time to market' often trumps the thorough code review and test phase.
The Boob Party

This is Linda Rosing. She's famous for getting a boob job, appearing on Swedish Big Brother and showing off her boobs and screwing everything left and right in front of the cameras, and then going off on one of these pub tours with promoters. Where the pub owners announce Linda Rosing or someone else from the docusoaps will be turning up for a drink.
So that was a while back and all that easy come easy go cash dwindles. Notice in the picture how the dress hides the fact that she has boobs bigger than Pam Anderson. You can't have big boobs like that and get into parliament - which by the way she's standing in front of in this pic from a typical Stockholm summer day.
Linda founded the 'Unique Party' at a press conference today, with a collection of Volvo workers, carpenters, single parents, and the like. Media sources say she's being directed from behind the scenes by Pirate Party emigrés.
Linda's proud she doesn't know anything about politics and says that's her third big advantage.
Ubuntu for Servers
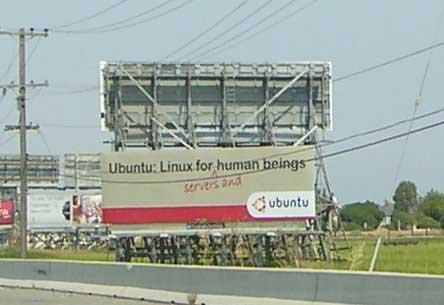
The Shuttleworth campaign to bring Ubuntu to the enterprise has begun. This is the first billboard for the campaign. Naturally it's in the US. In fact it's at the Ralston exit in Redwood City. Which makes it ironic. Ten years ago there was another presence in this town that people then believed in.
Redwood City seems to be a beautiful idyllic area. Lots of telephone poles and wires and billboards. Close to nature all the way over the pond there in the US of A.
Anybody for a chilidog and a deep fried Twinkie?
|