Home » Learning Curve » Red Hat Diaries
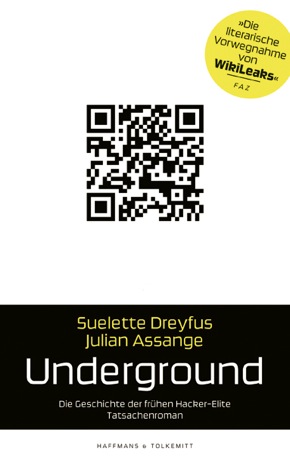
Süddeutsche: The Suelette Dreyfus Interview'Underground' to finally be released in German.
In the early 1990s University of Melbourne journalist and media scholar Suelette Dreyfus was part of the Australian hacker underground which included - known by the name 'Mendax' - WikiLeaks founder Julian Assange.
Hacking into university and telco networks back then got the police and the judiciary involved. In 1996 Assange was sentenced to AUD2100 in damages and a probation fine. Dreyfus and Assange were already researching their book, a task that would take them three years to complete. 'Underground' first appeared in 1997; now it's been translated into German for the first time.
The translation will be published by the German Verlage Haffmans & Tolkemitt.
Niklas Hofmann interviewed Suelette for Süddeutsche.
Q: In your book you try to describe the hacker scene as something genuinely Australian. Is this also true of WikiLeaks?
A: Absolutely. The interesting thing about WikiLeaks as well as about the early Australian underground is the attitude that not all authority is right and that it is something you have to rebel against. I describe the embryonic version of that in 'Underground'. We see a significantly enhanced version of that in WikiLeaks and in [hacker group] Anonymous. The politicisation of youth on the Internet is a real occurrence. This is the unifying theme, ranging from early underground to this day. We now have a youth culture that is very amorphous, difficult to pin down, very agile, highly mobile, and very adaptable. And this was also true for the early underground.
Q: How political were the early hackers back then? Everything sounds very playful in the book as if they were simply trying to invade any computer network they could get into.
A: There were traces of an early politicisation in a number of hackers I interviewed. Take for example the wanker worm which one might call the world's first politically motivated computer worm, or the first worm with a political message. That was a pretty significant milestone. For it was quite clear that the author or authors of this worm rejected the authorities that promoted nuclear energy. So they made fun of, made a kind of satire of it, as a clear sign of rejection. That was fun because the worm mostly played a trick on the authorities. It forced his way into the networks of NASA and the US Department of Energy and acted as if it would remove large amounts of data although nothing like that happened. All the data was still intact but some people might have had heart attacks which also was perhaps a little harsh. The same politicisation was also found in [Assange's hacker group] the International Subversives.
Q: In the book you quote Julian Assange as saying that he considered technology as a change agent. Was this the case back then already?
A: He pretty much saw that already at a young age. He could see absolutely clearly the direction in which technology would push things. That does not necessarily mean that he had a vision of WikiLeaks. But he certainly had a technological vision. The special thing about technology is that it enhances the ability to send information inexpensively to of a large number of people and that it provides better information than other sources. Julian has a very sharp technical mind and that is why efficiency was always very important to him. I once observed him as he packed boxes for moving. Most people just throw their stuff in the boxes. But Julian grabbed a box and when even the smallest space in the box was free, he'd unpack it. No matter how small the free space in the box was, no square in the box should be wasted.
Q: That sounds in fact like a technical mind but it is also somewhat surprising. For various other reports on Julian Assange - for example the book of Daniel Domscheit-Berg or the portrait in the New Yorker by Raffi Khatchadourian - interestingly also described how he moved and emphasised that he simply takes a case and throws things in.
A: That's a different matter. The difference is that he has a technical mind which sets in when a mystery must be cracked which he deems worthy to be solved either because he is doing something for society or because it sharpens his mind. Then he focuses on it. In this case, the boxes were a riddle. But his mind is focused on technical efficiency and that has something to do with the scalability of information. He does state that if one wants to achieve a positive change in the world, it must be done in a way that is scalable.
The only way to make something very large scale which is also affordable is with information. I think this is the point which was important for him when he founded WikiLeaks. You can earn a billion dollars with an Internet startup that actually works and then use the money to provide people in the poorest countries of the world with food. But will that really cause a social change in the long run? Medium term it will alleviate much suffering and this is important. But it does not necessarily set the technical screws for an optimal solution. Julian's mind is technical in the sense that he is concerned with optimisation. Whether it is optimising available space in a moving box or the optimisation of social change for the better.
Fear of the Unknown
 Q: How political was Assange at that time? Q: How political was Assange at that time?
A: As long as I've known him, he has been interested in issues of justice. Also, he always believed that it is unreasonable to hack just for the sake of hacking. That there were more important things in life. He has always been committed to society offline.
Q: In the book it seems strange that you describe some hacks in extreme detail and in the description of court cases you quote entire passages from the record. Does this level of accuracy come from Julian Assange or from you?
A: From both of us. We literally went through tens of thousands pages of documents - telephone recordings, listening logs, court records, witness statements. You have to provide readers with a degree of detail so they have the confidence that what is described is true. That can only come from the original documents. Parts of it must be in the text. You can't just do it with footnotes because then the evidence is not really accessible to the reader.
Q: That seems a like a foretaste of the scientific journalism that Julian Assange is endorsing today.
A: That's right. Julian calls it 'scientific journalism'. In essence it's about delivering unfiltered information that people can verify themselves. That was by all means very important during the writing of the book.
Q: You could also get the impression that WikiLeaks is a departure from Julian Assange's hacker roots. Contrary to the public impression, none of the major scoops by WikiLeaks have come to light due to hacking. One would think that someone with his hacking skills would make more use of them.
A: It's not just about technical skills. Hacking in the oldest sense of the word does not mean anything illegal at all. What is meant is that someone takes a difficult problem, finds a clever technical solution for it, and implements it. That is the original meaning of hack and hacker. In this sense Julian took the old definition of hacker and transferred it to WikiLeaks. It's a clever technological solution to the difficult problem of whistleblowing. And that's really a difficult problem. Very early on he had an interest in making a publication platform available for whistleblowers and for groups campaigning for justice.
Q: When you describe the time when the Australian police together with the FBI went after the hackers, it sometimes sounds a little bit like cops and robbers. On the other hand, you describe the time as traumatic for the hackers. Sometimes one gets the impression that the treatment by the police was not as bad as feared by the hackers. Was there self-created paranoia?
A: Yes, especially a fear of the unknown. They'd heard from other people in the Underground who'd been raided - horror stories were circulating that were much worse than the reality. There were also some really tough cops. But in most cases, the reality was probably not as bad as it was perceived by them from a distance. At night in the dark, when there were strange noises in their backyard, when their parents had gone out and they had spent their time hacking until three o'clock in the morning and they were exhausted. These are moments when you can start to get scared.
Victimless Crime
Q: Most of them - including Julian Assange - got off with relatively light sentences, monetary penalties, partly on probation. This doesn't seem terribly dramatic. What was traumatic about it?
A: What was really extremely traumatic for the hackers was that the police seized their computers. Computers were very different then from what they are today. You could not just go out and buy a replacement. Most of them did not come from wealthy homes. To take away their computers was like cutting of an arm or a leg. The computers were really a core of their personality. They allowed them to communicate with the online community and to have their own identities in this community. So it was a loss of identity and of community. It was also a loss of information. Most were information junkies, all highly intelligent. And they did not get current information because they had no access. It was just like denying somebody who is very inquisitive access to all libraries. They were also cut off from their friends who had the same interests. It was like putting duct tape over their mouths since they could not really talk to these people anymore.
The only tool to express their own form of creativity had been taken from them. In some respects this punishment was far worse than anything they could have suffered in court proceedings, during interrogations, interviews, or in prison. Much worse.
Q: They knew they were doing something forbidden and almost waited for an arrest. However, it seems that they would have rather expected to be treated as prisoners of war - at eye level - than be treated as common criminals.
 A: This is partly because only a few of them saw themselves as criminals. Most of what they did, though not everything, were victimless crimes. This especially applies to the elite amongst them. They didn't participate in fraud or in the theft of credit card data. They read information which they were not supposed to have read. They made copies of it for their own private circles. So to them it was probably a surprise that they were treated like criminals.
A: This is partly because only a few of them saw themselves as criminals. Most of what they did, though not everything, were victimless crimes. This especially applies to the elite amongst them. They didn't participate in fraud or in the theft of credit card data. They read information which they were not supposed to have read. They made copies of it for their own private circles. So to them it was probably a surprise that they were treated like criminals.
But there is also another element, which is already a hint of what we are experiencing today. They felt compelled to break into the networks of universities and the like to obtain access to information they thought should be freely available. And which is freely available today. Back then, their view was that this information should be available to us, it is not, so we go and get it, for we are the young generation and we have a right to it.
Q: You have just described this playful element of youthful rebellion. But at what point does it get really political?
A: Hackers often stumble upon things. They told me they were once in the system of a software company where they found the proprietary code of a rival company. And they were pretty sure that the competitor didn't allow that. Naturally they thought that was funny but they also recognised the unethical side about it. They couldn't shout that out to the world of course. But they saw it and noticed it.
And I think if you're a hacker and moving in this environment, then you begin to look under the surface and behind the facade of all this, of what we see every day but do not know. You can see the real power structures, see who really has power within these structures, how they use that power, how they get this power and keep it. And that is not always happening in an ethical way.
Q: So this is the same thing WikiLeaks cables do? Offer a peek into a world in which perhaps not the opposite of what we think is true but which is different nonetheless?
A: There are different levels. But take for example the Arab spring. I'm pretty sure the people in Tunisia, Libya, and Egypt knew there was a lot of corruption there. Perhaps they lacked the real evidence, perhaps they didn't know how widespread it was, perhaps they didn't realise how corrupt the people who have all the money and power really were. Suddenly the cables brought them the unfiltered truth about the extent of corruption and other dirty things, torture and so on. To me that seems to be a turning point.
Hillary Clinton indeed likes to say it was Twitter and Facebook that caused the unrest. The Egyptian protesters have compiled a very good, short manual explaining how to do it, how to change a regime. And the first thing on page one and again on the last page is: do not use Facebook, do not use Twitter!
So I find it surprising the US Secretary of State says it was Twitter and Facebook that triggered the revolutions. No - it was the truth that caused the revolutions. The unfiltered truth. And that truth came from the cables.
Translation work by the gracious LLC.
See Also
Suburbia: Underground Downloads
Süddeutsche: Im Untergrund mit Assange
Haffmans & Tolkemitt: Suelette Dreyfus und Julian Assange: Underground
WikiLeaks: Support WikiLeaks
The Police Protocol (Translated)
Rixstep: Assange/WikiLeaks RSS Feed
Radsoft: Assange/WikiLeaks RSS Feed
|