Home » Learning Curve
Spyfiles & YouYou'll be careful, won't you? Of course you will.
LONDON (Rixstep) — Recent revelations by WikiLeaks that hundreds of companies are spending billions to find ways to spy on you through your iPhone, Blackberry, or Gmail account serve as a wakeup call. You need to know a few things about what's going on to protect yourself.
Attack Vectors
Most of the video clips available so far indicate the 'bad guys' are 'trojanising' systems rather than attempting to infect them through vulnerabilities. This might be a gross oversimplification but it does serve to shed light on one very important aspect of your survival: keep your head. If the 'bad guys' are going to try to trick you through a bogus iTunes update, then don't fall for it.
For no one can help you - or an IBM z-series system administrator - if you're that easily fooled.
But starting now, it's obvious the attack you never see could come from anywhere. So be prepared for it.
Ingress
The only way the 'boys with toys' can get at you (if they haven't already) is by you downloading stuff they send your way. Remember that old paradoxical Apple aphorism?
'Never run unknown or untrusted software.'
- Apple
How do you get by that?
Admins have an easy time of it - they set up isolated test machines. Machines they can wipe and reinstall after every test. Odds are you don't have that same luxury (or their expertise). The only way around that for you is to make sure you're watching your new software very carefully. And there's only one known way to do this at the present time: Tracker.
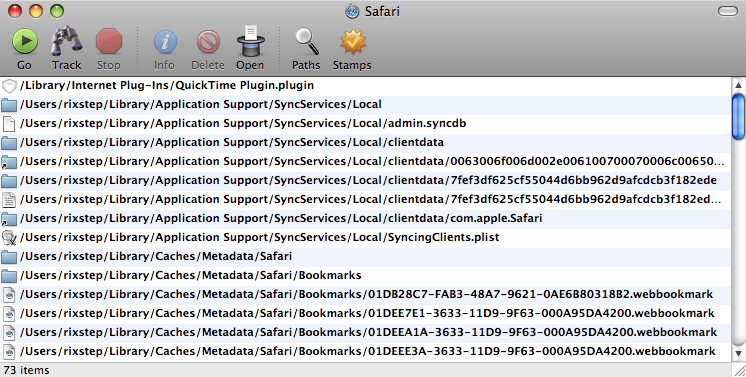
The free Xfile Test Drive includes Tracker. Or at least a streamlined version of it. It might temporarily be enough for your needs.
Or you could do like John Gruber once did: save 'before' and 'after' text files of every file you have on your entire hard drive, then manually inspect the files afterwards.
Your choice.
And please note: the 'App Zapper' class of tools won't help you here. They only remove things, and they do a lot of guesswork as well. Tracker sees (and records) everything that happens on disk to your entire file system.
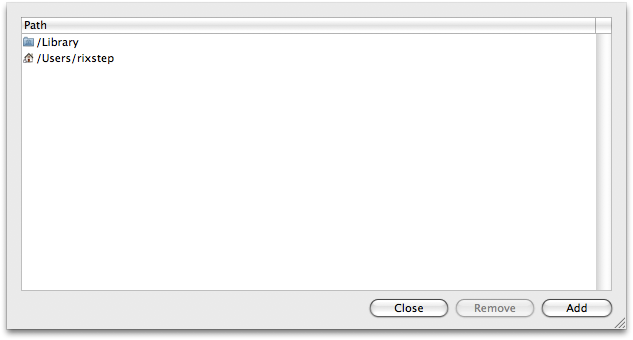
You can limit the areas of your hard drive to be scanned by Tracker. Default today are the hives /Library, /private, and /Users/[YOU] (you). This is a convenience only. Tracker can just as easily track everything on your hard drive. With today's 'Spyfiles' climate, it's probably best to check everything.
So get the Xfile Test Drive and start using Tracker. Remember: the Xfile Test Drive version is free.
Connections
Who's connecting to your box? For what reason? Do you know? You might want to check your firewall settings, but this is a complex task.
$ sudo ipfw show
You can also use a utility like this. GD.

GD keeps a running tab on your open Internet connections and even has an accessory popup that keeps a log of your connection history. For example: it's been recently discovered that Twitter code generates connections with the Swedish TeliaSonera - and the Swedish FRA can thereby track all your activities - and one very strange company claiming to be a 'content delivery provider', with domain registrations in five countries, but with web servers exclusively in Israel.
What's up with that?
At any rate: GD can get you there so you detect stuff like that.
Another good utility to take advantage of is Apple's own Activity Monitor. Particularly the 'Open Files and Ports' tab.

Pluck out the files you see there and go through them. It can be a lot of hard work but it can be worth it.
Egress
Egress is how the 'bad guys' phone home: they have to send data out from your computer. Either set up a firewall so you can control and monitor what flows out, or get a utility like Little Snitch. GD will also show you what's leaving your computer, but you might want more control over what actually passes through.
Of course the ultimate bruiser is Xframe, but again that won't control the traffic. But it will sniff each and every packet going in and out. Check the screenshot here. That should give you an idea of what's going on.
Innocent Observations
- You have to be able to tinker to protect yourself. Apple aren't going to tinker much for you and their mobile devices specifically disallow all such software. So as Julian Assange said: 'you're screwed'.
- Stop wanking about with Finder. You need a good file manager. You need full and unfettered access to your entire hard drive. If you want to lug the colossus Path Finder around with you, then fine. But get something. Those 'boys with toys' love it when you use Finder which won't show you half your file attributes, a tenth of your directories, or any of the other good stuff they so much love themselves. Want to know why Windows is such a haven for malware? The Registry. What's the difference on OS X if Apple won't let you see onto your hard disk?
See Also
WikiLeaks: The Spyfiles
Rixstep: GD: The Better Man
Rixstep: Tracker: Why chance it?
Rixstep: The Free Xfile Test Drive
Learning Curve: First Time Tracker
Rixstep: Xframe: The Packet Sniffer
IBM: System z (zEnterprise)
|