Home » Learning Curve
Introduction: What's New in CLIX 2.4.0.0?Free High Sierra standalone release 11 April 2018. A first look.
ORANGE WALK TOWN (Rixstep) — CLIX 2.4.0.0 is the standalone version of CLIX 2.4.0 which ships with the ACP and with the Xfile pack. Version 2.4.0.0 finally brings the free version up to speed.
As this is an application meant to run on most any version of Apple's OS X (macOS) it's been tested on platforms ranging from the latest ('High Sierra') to August 2009's 'Snow Leopard'.
This piece will cover some of the changes to CLIX.
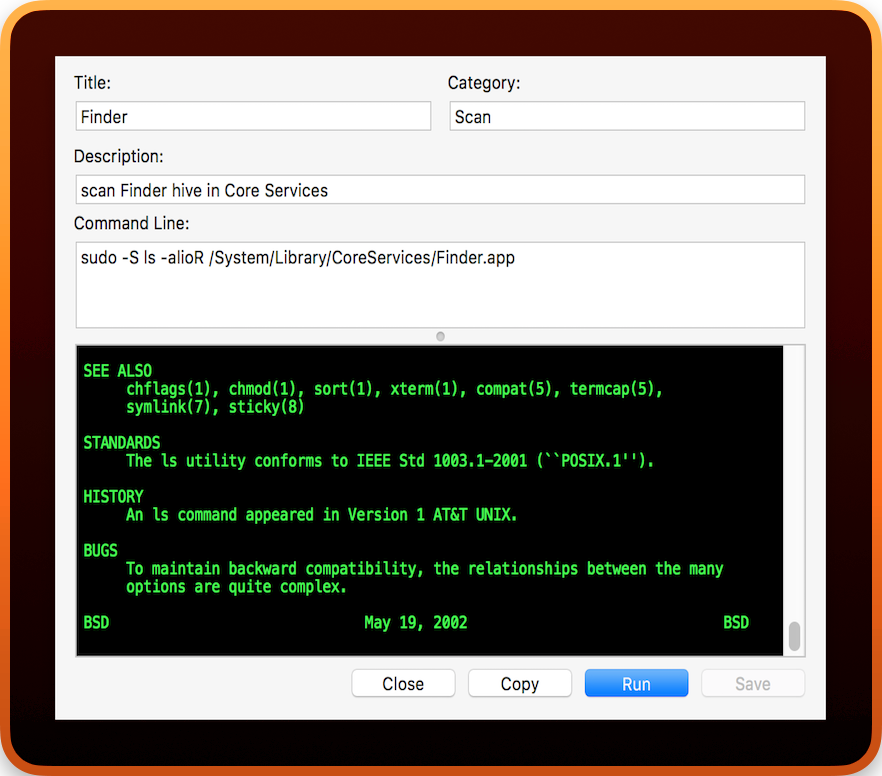
Orange is the new CLIX
CLIX now ships with five (5) application icons, including the very first icon, some 14+ years ago. The idea is always to convey the concept that CLIX is a 'graphical' (and an extensible) take on the Unix command line.
The five icons are located within the CLIX application bundle, at Contents/ICNS. The default icon has a hint of orange to match the default output foreground colour.
Designated colours in the output field now admit of an 'alpha' value, so transparency (opacity) can be controlled, with '0' representing full transparency and '255' representing full opacity.
The default colour scheme for the output field, as the CLIX command sheet, was updated for the first time ever. The font used previously, Monaco, is replaced with the more modern Menlo.
Houdini
Erik Weisz, or Harry Houdini, is still in residence, protecting you from unwanted interlopers. His technology has been updated to take advantage of the latest in cryptology.
Note that attempting to secure an application bundle with Apple's root certificate does not work: hacking such a bundle on Apple's macOS is child's play. CLIX, on the other hand, is sealed - from the inside - by a lock placed on the outside. If the lock should be broken or tampered with, if any attempt be made to hack the CLIX binary, CLIX will simply refuse to launch, or, in the case where it has already been launched, refuse to carry out any critical operations.
These operations include invoking the sudo passphrase sheet and the command sheet. The internal representation of your passphrase is shredded, its storage freed, and any exposed secure text fields for the passphrase are immediately 'zapped'.
[No matter the circumstances, or the number of open document windows, CLIX allows only one passphrase sheet at a time. This is for your security.]
CLIX/Houdini will also make sure your passphrase is never insecure (readable).
The Zero Effect
Prior to running a command, Houdini will make sure the command is not 'piped' through by a rogue interloper. It does this by traversing the system process table, to make sure it is itself the originator of such a request.
Also prior to running a command, Houdini will remove any remaining sudo timestamps - regardless of user settings - so that your sudo passphrase must be submitted when needed, no matter there otherwise be a so-called 'grace period' (normally set to five minutes).

After completing a command, CLIX/Houdini performs an asynchronous operation to again remove sudo timestamps.
In order to safeguard against $PATH hijacking, something not addressed by the bash developers, CLIX/Houdini only recognises the $PATH value resident in read-only kernel memory.
[The ACP Text Services (not included in the free CLIX) provide a means to expand commands to full paths according to the 'userland' $PATH.]
CLIX/Houdini also monitors the sleep state of your system, and removes all vestiges of your passphrase when needed. There's normally a (very) minimal 'window' where other applications (such as Terminal) can, with sudo itself, fall victim to an interloper prepared to 'act fast'. CLIX/Houdini doesn't allow this.
CLIX/Houdini can also alert you (and ask your permission) any time a command process is prompted for your passphrase.
5,745 Commands
Rather than packaging close to 6,000 (six thousand) commands with its download, CLIX 2.4.0.0 provides links, within its own documentation, to additional files. This number can be expected to grow further over time.
The legacy commands are provided 'as is'.
Augmented Bibilography
CLIX 2.4.0.0 contains an augmented bibliography on CLIX, Unix, the defaults system, and other topics of general interest.
About RixstepStockholm/London-based Rixstep are a constellation of programmers and support staff from Radsoft Laboratories who tired of Windows vulnerabilities, Linux driver issues, and cursing x86 hardware all day long. Rixstep have many years of experience behind their efforts, with teaching and consulting credentials from the likes of British Aerospace, General Electric, Lockheed Martin, Lloyds TSB, SAAB Defence Systems, British Broadcasting Corporation, Barclays Bank, IBM, Microsoft, and Sony/Ericsson.
Rixstep and Radsoft products are or have been in use by Sweden's Royal Mail, Sony/Ericsson, the US Department of Defense, the offices of the US Supreme Court, the Government of Western Australia, the German Federal Police, Verizon Wireless, Los Alamos National Laboratory, Microsoft Corporation, the New York Times, Apple Inc, Oxford University, and hundreds of research institutes around the globe. See here.
All Content and Software Copyright © Rixstep. All Rights Reserved.
See Also
ACP: CLIX Product Page
Learning Curve: Guerilla CLIX (September 2012)
Technological: Cult of Mac Discovers Unix (December 2012)
Industry Watch: CLIX 2.0.0.16 (January 2013)
Learning Curve: Mavericks Clicks (October 2013)
Industry Watch: CLIX 2.1 (November 2013)
Learning Curve: OS X Snake Oil (July 2015)
Industry Watch: CLIX: Sierra Elementary (1) (November 2016)
Industry Watch: RELEASE: CLIX for macOS (August 2017)
Developers Workshop: CLIX Untappable (January 2018)
Industry Watch: RELEASE: Orange is the new CLIX (April 2018)
|