Home » Learning Curve » CLIX: Legally Hacking
CLIX: Legally Hacking - IntroductionIt's still possible. On a Mac. You can still enjoy discovery.
Apple like to keep things hidden. Their OS might be based on open source, but they've never had any intention of keeping things that way. They licence their OS kernel from FreeBSD which has much more generous terms than Linux. The 'beast in Redmond' did the same thing - use FreeBSD Berkeley sockets code to get onto the Internet. Neither Apple nor Microsoft are required to reveal all their source code to FreeBSD. (Richard Stallman doesn't like that.)
There are still a lot of things one can do on a Mac. The popularity of CLIX seems to indicate there are a lot of curious wannabe hackers out there - people who through a healthy curiosity want to peek and poke just like the programmers and the admins do. The rewards can be significant.
CLIX started early on a morning when the dilemma of how to achieve a functional but flexible and infinitely configurable system tool was first discovered: build it as a simple flat database manager and give the data record's edit sheet additional capabilities. The first run-through of CLIX took 14 hours nonstop programming; after that the application was more or less complete and was released the same day.
But a lot has happened since. And CLIX evolved into being a hyper-secure system tool. CLIX 2.0.0.14 is now ready for the coming Mac OS X 10.7 Lion as things stand today. The small hitch had been a disappearing (and vital) Unix system call. The hitch has now been 'unhitched' and things are again proceeding according to plan.
CLIX is a Cocoa Application
CLIX is not the 5000+ commands included in the download. CLIX is the application and no more. CLIX would be just as valuable without those command files. Because the studious hacker will still know how to use the application properly. After all, it's simply the Command Line Interface for OS X.
But if Apple's Terminal.app is the default command line interface, what then is CLIX? And why choose CLIX over Terminal?
It might be a cool thing to watch a seasoned Unix admin fire off a command line of 250+ characters, see the consternation when character 141 is found to be wrong, and watch when the admin starts all over again. Various mechanisms have cropped up over the years to reduce the time and effort wasted in retyping lugubrious commands over and over again but none really took you very far. Then along came CLIX.
WORM
CLIX is a 'WORM' type of command line interface - 'write once, run many times'. Once you get a command line right the first time, you never have to type it in again. The very name 'CLIX' also hints at how the application works - there's less keyboard activity and more 'clicks'. It's perfectly possible to run an entire CLIX session without once using the keyboard.
A certain class of legacy Mac user seems to have a phobia about command lines anyway. After all, the Mac was the first PC running without one. And now that Bill Gates feels so chuffed his Windows can finally exist without one, it seems ironic that Apple's Macs introduce one for the first time.
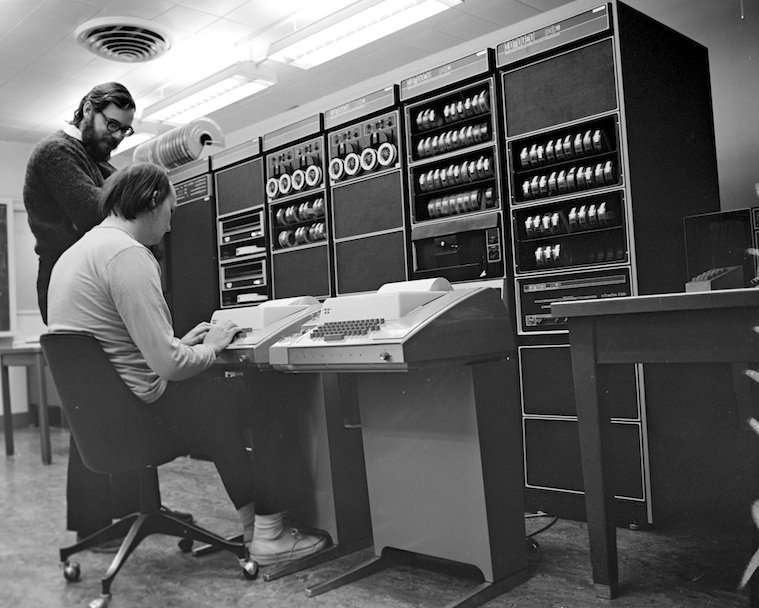
But Apple's current computer OS is not the old Apple OS and thankfully it's not Windows either. It's a direct descendant of the best of the best - Ken Thompson's and Dennis Ritchie's Unix from Bell Labs in New Jersey, the achievement they won the 1998 National Medal of Technology for (handed to them in the White House by Bill Clinton).

And the command line is always there whether you want it to be or not, whether you see it or not. All applications in Unix start the same way - with a command line.
int main(argc, argv) {
}
All applications anywhere start the same way (although the parameters can of course differ). The command line is merely the exposed interaction between processes, between applications. It gives you the opportunity to 'jump in' and do things your way.
There were no graphics interfaces in widespread use in the beginning of the 1970s. Computer hardware wasn't advanced enough. Ken Thompson deliberately designed the Unix commands to be as cryptic as can be - not because he was esoteric but because he didn't want to have to type too much.
Mostly he removed vowels from ordinary command words. 'Remove' became 'rm'. 'Move' became 'mv'. 'Copy' became 'cp'. And so forth.
Ken was once asked if he would change anything if he could do it all over again and he famously quipped 'I'd add an 'e' to the end of create()'. creat() is a system API for creating files and he even chopped the 'e' off the end. But this wasn't a fetish on Ken's part - this was a purely practical matter. To improve workflow.
Look into the four standard locations for Unix command line programs and you'll find a lot of the same thing. From /bin:
| bash | | Bourne again shell | | mkdir | | make directory |
| cat | | catenate | | ps | | process status |
| chmod | | change mode | | pwd | | print working directory |
| launchctl | | launch control | | rmdir | | remove directory |
| ln | | link | | sh | | shell |
The same thing in /usr/bin, /sbin, and /usr/sbin. These command line programs are the stuff of Unix on Mac OS X 10.6 - all 1,028 of them. 1,028 programs. With much more than 1,028 possibilities. Many of them are legacy Unix dating 'way back'; many are Apple's own (or inherited from NeXT) and they're all there because they're supposed to be used. By you.
You don't have to be a systems or device driver programmer to be a hacker. Hacking is a state of mind more than a level of expertise. Hacking is like cooking: you create your own meals from scratch and you experiment because it's fun and because it's hopefully beneficial. It's the experimentation that's important. That's how progress comes about.
And as Bell Labs programmer Brian Kernighan pointed out time and again in his own books, experimentation leads to helpful tools which in turn make it easier to keep on experimenting, which in turn leads to even more (and even better) tools, and so forth. And things keep on cycling in that fashion. That's what it's about - improve your workflow, find out as you do that there are further ways to further improve that workflow, so you keep pushing and prodding, and you end up finding out even more about your workflow (and your system) and so forth.
cd ~ (AND DON'T WANDER OFF)
Apple have 1.028 Unix commands on disk in Mac OS X 10.6 Snow Leopard but they don't really like that. They'd really rather you knew nothing about these files at all. They've worked hard to make it as difficult as possible for you to get to them. They try to keep you closed into your tidy own 'home area'. And there's also a good reason for this as well as several bad: they don't want to frighten off new adopters. First timers confronted with an array of 1,028 command files? Where to start? Their tired eyes would start to water over.
But the files are there, and they're there for the taking, and over 150 Apple engineers use CLIX themselves, so there must be something to it. Right?
Future articles in this series may hopefully review (for the umpteenth time) exactly how one goes about 'legally hacking' one's own Mac. For there's a very simple (and innocuous) way to go about it.
Unix is basically a simple operating system but you have to be a genius to understand the simplicity.
- Dennis Ritchie
See Also
Wikipedia: Hacking
Dennis Ritchie: An amusing photo
Dennis Ritchie: Letter from Washington
National University of Singapore Hackers
Rixstep Industry Watch: CLIX 2.0.0.14
Learning Curve: 1st Time CLIX?
CLIX: The #1 Power Tool for OS X
Google: CLIX Articles at Rixstep.com
Learning Curve: CLIX False Beginners
|