Home » Learning Curve
Facebook AgainThese are not mere accidents.
MENLO PARK (Rixstep, Radsoft) — 'While journalists and netizens are distracted digesting the redacted 400-plus-page Mueller report, released within the past few hours, today will be a good day for spin doctors to bury bad news', writes Iain Thomson of El Reg.
'And Facebook just couldn't pass up on the opportunity.'
https://www.theregister.co.uk/2019/04/18/facebook_instagram_passwords/
'One hour before the long-awaited dossier by Robert Mueller - special counsel of the investigation into Russian interference in the 2016 United States presidential elections - began circulating in Washington DC and beyond, Facebook quietly amended an online press release it issued in March.'
Note that they amended an earlier press release - they're trying to sneak in under the radar and still come off pure as the driven snow.
'The press release in which the antisocial network admitted to storing hundreds of millions of its user account passwords in plain text in log files on its servers that were accessible by its internal staff. A rather clumsy move.'
'Clumsy' is kind. In fact, there's no 'clumsy' about it. As with Twitter a few months back, this is deliberate, and there are no two ways about it.
Note that this 'clumsy' move also applies to their Instagram colony, with (at least) millions of accounts affected. And, in this day and age, such behaviour should be processed with a criminal complaint. It won't happen, of course, but it should.
For this is no mistake, no blooper, no oversight, or anything of the kind. This is deliberate.
Here are the links to the FB announcement, if you want to waste your time.
https://newsroom.fb.com/news/2019/03/keeping-passwords-secure/
http://archive.is/Ww0Wb
As for this nonsense, don't believe it:
'Our investigation has determined that these stored passwords were not internally abused or improperly accessed.'
Judging from the comments at El Reg, some people assume this is a 'programming error'. And the riffraff in the mosh pit are too busy following the show to pay any attention.
How Passwords Are Encrypted.
Start here if you feel up to it.
https://en.wikipedia.org/wiki/Cryptographic_hash_function
What's used is 'a mathematical algorithm that maps data of arbitrary size to a bit string of a fixed size and is designed to be a one-way function, that is, a function which is infeasible to invert'.
Note the 'one way'. Now go back and note it again.
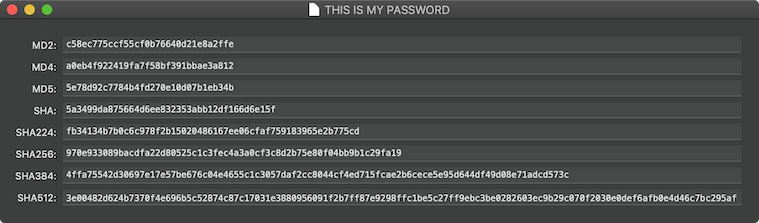
The above graphic, from our own utility MD, shows the message digests for the password 'THIS IS MY PASSWORD'.
MD2: c58ec775ccf55cf0b76640d21e8a2ffe
MD4: a0eb4f922419fa7f58bf391bbae3a812
MD5: 5e78d92c7784b4fd270e10d07b1eb34b
SHA: 5a3499da875664d6ee832353abb12df166d6e15f
SHA224: fb34134b7b0c6c978f2b15020486167ee06cfaf759183965e2b775cd
SHA256: 970e933089bacdfa22d80525c1c3fec4a3a0cf3c8d2b75e80f04bb9b1c29fa19
SHA384: 4ffa75542d30697e17e57be676c04e4655c1c3057daf2cc8044cf4ed715fcae2b6cece5e95d644df49d08e71adcd573c
SHA512: 3e00482d624b7370f4e696b5c52874c87c17031e3880956091f2b7ff87e9298ffc1be5c27ff9ebc3be0282603ec9b29c070f2030e0def6afb0e4d46c7bc295af
Eight algorithms are used: MD2, MD4, MD5, SHA, SHA224, SHA256, SHA384, and SHA512. Other algorithms can be available outside the system.
Crafting those algorithms isn't easy. The idea is to be able to create such a mishmash - always of the same predetermined length - that is totally unique, or, as they say in the business, 'collision-free' - in other words, no two input values can ever produce the same result.
Collisions are discovered from time to time - there's no way other than heuristics to show that an algorithm is 'most likely' safe.
But the key point here is that your password is immaterial.
Your Password Is Immaterial.
That's right: the system, which of course is based on user protection, precludes the need for the remote host (eg Facebook, Twitter) to ever need or even be remotely interested in your password.
Very early IBM systems did use 'one on one' encryption for passwords, but that was abandoned over half a century ago. Along came DES, watered down from 64-bit to 56-bit at the behest of the NSA who wanted to have a fighting chance of cracking it with their computers in Fort Meade.
Now if the NSA found password cracking so daunting, how do you expect Facebook able to do it with such ease?
Transport Layer Security
Transport Layer Security, or TLS for short, is the current cryptographic protocol used to provide security on the Internet.
One of its primary goals is to thwart the so-called Man-in-the-middle attack. Put simply, TLS - as predecessor SSL (Secure Sockets Layer) - ensures that you, the user, are alone in the communication channel being used to, for example, authenticate you to a remote server, such as Facebook's.
So what happens - what should happen - when you log in to Facebook?
- You access a Facebook server.
- You are prompted for your user ID and your password.
- This data is sent through TLS to the Facebook server.
- Facebook receives your data and notes your user ID.
- Facebook creates a message digest of your submitted password.
- Facebook looks up your user ID in Facebook's own records.
- Facebook compares your submitted encrypted password to their own version.
By its very nature, this authentication system is not interested in your unencrypted password. Your password is immaterial.
The only way Facebook could possibly have user passwords is if they are deliberately harvesting them.
That's it.
So that means that Facebook (and Twitter, as is already known) inserted new code to deliberately harvest your passwords. Operative word? 'Deliberately'. This was no programming bug, or error, or mistake. As with Twitter, this was deliberate.
Ramifications
The conclusion that Facebook (and Twitter too, don't forget) deliberately harvest passwords is that they want them. There's hardly a maintenance issue here. The risk for mistakes is too great.
So why do they do it? Why do both Facebook and Twitter do it?
Perhaps more importantly: how do users guarantee that they're not doing it?
Code-auditing would be egregious, and it's too easy to deceive code auditors.
Perhaps the fear of Chapter 11 can scare them.
About RixstepStockholm/London-based Rixstep are a constellation of programmers and support staff from Radsoft Laboratories who tired of Windows vulnerabilities, Linux driver issues, and cursing x86 hardware all day long. Rixstep have many years of experience behind their efforts, with teaching and consulting credentials from the likes of British Aerospace, General Electric, Lockheed Martin, Lloyds TSB, SAAB Defence Systems, British Broadcasting Corporation, Barclays Bank, IBM, Microsoft, and Sony/Ericsson.
Rixstep and Radsoft products are or have been in use by Sweden's Royal Mail, Sony/Ericsson, the US Department of Defense, the offices of the US Supreme Court, the Government of Western Australia, the German Federal Police, Verizon Wireless, Los Alamos National Laboratory, Microsoft Corporation, the New York Times, Apple Inc, Oxford University, and hundreds of research institutes around the globe. See here.
All Content and Software Copyright © Rixstep. All Rights Reserved.
|